%20(93).png)
Proxy Browsers: How They Work, Key Risks, and How to Use Them Safely in 2026

What Is a Proxy Browser?
A proxy browser is a browser or application that routes your HTTP/HTTPS internet traffic through a proxy server instead of connecting directly to websites. This intermediary server acts as a virtual pipeline between you and the destination website, handling requests on your behalf.
The distinction between a “true” proxy browser and a standard browser using system-level proxy configurations is important. Dedicated proxy browser apps come with built-in proxies, integrated profile management, and fingerprint spoofing capabilities. In contrast, standard browsers like Chrome, Mozilla Firefox, or Microsoft Edge can be configured with proxy settings through operating systems settings or browser extensions, but they lack the specialized features that purpose-built tools offer.
When you access websites through a proxy browser, the destination website sees only the ip assigned by the proxy server—not your original ip address or actual location. This ip masking mechanism is what makes proxy browsers valuable for both privacy-conscious individuals and business users who need to simulate access from different geographic regions.
From 2020 through 2026, adoption of proxy browsers has surged dramatically. Use cases now span ad verification teams checking campaign delivery across regions, retailers conducting price monitoring on competitor sites, sneaker resellers securing limited releases, and marketing agencies running multi account management for social media campaigns.
SimplyNode’s residential and mobile proxies can be integrated into many popular proxy browsers and anti-detect browsers for legitimate business use, providing the IP diversity and geo-targeting precision that these workflows demand.
How Proxy Browsers Work (Technical Overview)
Understanding how proxy browsers work requires following the path of a single web request from your device to the target server and back again.
Here’s the step-by-step process when you open a site through a proxy browser:
- DNS Lookup: Your proxy browser initiates a connection and resolves the destination website address.
- Request Formation: The browser constructs an HTTP or HTTPS request for the target page.
- Proxy Forwarding: Instead of sending this request directly, the proxy browser routes it through the configured proxy server.
- IP Replacement: The proxy server replaces your real ip address with its own IP (residential, mobile, or datacenter) before forwarding the request.
- Server Response: The target website processes the request as if it originated from the proxy’s location and returns data.
- Response Delivery: The proxy server receives the response and passes it back to your browser.
Websites see the proxy’s IP, not your home or office address. If you’re using residential proxy ips sourced from real ISP networks, the connection appears indistinguishable from a regular consumer browsing session.
Modern ssl encryption and HTTPS protocols ensure that data remains protected in transit. As of 2026, proxy protocols have evolved to include HTTP, HTTPS, and SOCKS5 options. SOCKS5 offers greater flexibility, supporting UDP traffic and providing more versatile proxy configurations for various applications beyond simple web browsing.
Sessions represent another critical concept. Rotating sessions change your IP with each request or at specified intervals—ideal for web scraping at scale where you need to avoid rate limits. Sticky sessions maintain a single IP for minutes or hours, which works better when you need session persistence for logins or maintaining shopping carts.
Forward proxies (what proxy browsers use) sit in front of clients to anonymize outgoing proxy traffic. Reverse proxies, by contrast, sit in front of web servers to handle incoming requests—you’ll encounter these as CDNs or load balancers, but they serve a different purpose entirely.
Legitimate Use Cases for Proxy Browsers
Proxy browsers are dual-use tools with many fully legal and beneficial applications. The same technology that enables circumvention also powers critical business operations across industries.
Online Privacy Protection
Individuals use proxy browsers to reduce tracking exposure, especially on public Wi-Fi networks, shared computers, and when traveling. By routing browsing data through intermediary servers, users prevent websites and advertisers from building accurate profiles based on their real ip address and location.
Geo-Restricted Content Access
Testing how services appear in different regions is essential for global businesses. Concrete examples include:
- Verifying a US-only streaming offer renders correctly from Europe
- Checking localized e-commerce pricing across Asian markets
- Confirming that video websites display region-appropriate content
Multi-Account Management
Marketers and agencies routinely manage multiple accounts across social platforms, marketplaces, and advertising networks. Without proxy browsers that provide unique browser profiles and distinct IPs, platforms quickly flag these accounts as related and impose bans. Proper proxy setups enable teams to manage multiple accounts without triggering automated tasks that detect suspicious patterns.
Business Data Collection
Web scraping, price monitoring, and market research require accessing popular websites at scale without getting blocked. Teams use proxy browsers connected to robust residential and mobile proxy pools to gather competitive intelligence, track pricing trends, and collect publicly available data for analysis.
Compliance, QA, and Ad Verification
Organizations verify how ads, landing pages, and legal notices render in specific countries or cities. This compliance testing ensures that marketing campaigns meet local regulations and that restricted content warnings display appropriately.
SimplyNode’s city-level geo-targeting and ethically-sourced IPs make these use cases more accurate and policy-friendly, reducing the risk of using low-quality proxy ips that might be flagged or banned.
Common Types of Proxy Browsers and Tools
The term “proxy browser” encompasses different tools depending on implementation: full browsers with built-in proxies, anti-detect applications, web-based proxy sites, or browser extensions that add proxy functionality.
Stand-Alone Anti-Detect Proxy Browsers
These specialized tools combine fingerprint spoofing with massive profile management capabilities. Each browser profile maintains unique characteristics—screen resolution, timezone, fonts, WebGL parameters—making it appear as a distinct device. Growth marketers and automation teams favor these for running dozens or hundreds of accounts simultaneously.
Standard Browsers with Proxy Managers
You can configure Chrome, Brave, or Mozilla Firefox with proxy manager extensions that assign different IPs per profile or tab. This approach uses familiar browsers while adding proxy capabilities through software installation of extensions. It’s more accessible but offers less fingerprint customization than dedicated anti-detect solutions.
Mobile Proxy Browsers
Android and iOS apps route proxy browser traffic through mobile networks, often using 5G, 4G, or LTE connections. These prove valuable for testing mobile-specific experiences and mobile ad campaigns where desktop proxies would produce different results.
Proxy Type Considerations
In the context of proxy browsers, the type of proxy matters significantly:
- Residential proxies: IPs from real ISP networks, appearing as genuine home users
- Mobile proxies: IPs from cellular carriers, ideal for mobile app testing
- Datacenter proxies: Fast but easily identified by sophisticated detection systems
As of 2026, residential and mobile IPs look far more like real users to websites, making them preferable for high-value tasks. Most proxy browsers perform best when connected to reputable networks like SimplyNode rather than relying on unknown free proxy services.
Why Malicious Proxy Browser Traffic Is Hard to Detect
Detecting malicious proxy traffic presents significant challenges because it often appears identical to legitimate user activity originating from normal ISPs and mobile carriers.
Residential IP Camouflage
Residential and mobile IPs come from real consumer networks. Simple IP blocklists or hosting-based detection fail when attackers route through the same IP ranges that genuine customers use. A login attempt from a residential IP in Chicago looks the same whether it’s a real user or an attacker using a proxy.
Behavioral Mimicry
Sophisticated attackers go beyond IP masking. Automated frameworks simulate realistic behavior:
- Random mouse movements and scroll patterns
- Variable delays between actions
- Rotating user agents and browser fingerprints
- Natural typing speeds for form inputs
These techniques defeat basic heuristics designed to catch automated tasks and bots.
Encryption Barriers
TLS/HTTPS encryption—now standard across virtually all websites in 2026—prevents deep packet inspection of content. Defenders must rely on metadata and behavioral patterns rather than examining actual request contents.
Geographic Distribution
Constantly rotating IPs across many countries and cities hides patterns, especially when malicious traffic blends with legitimate proxy traffic from the same networks. An attacker accessing a site from 50 different countries over an hour might be scraping data or might be a legitimate enterprise running ad verification.
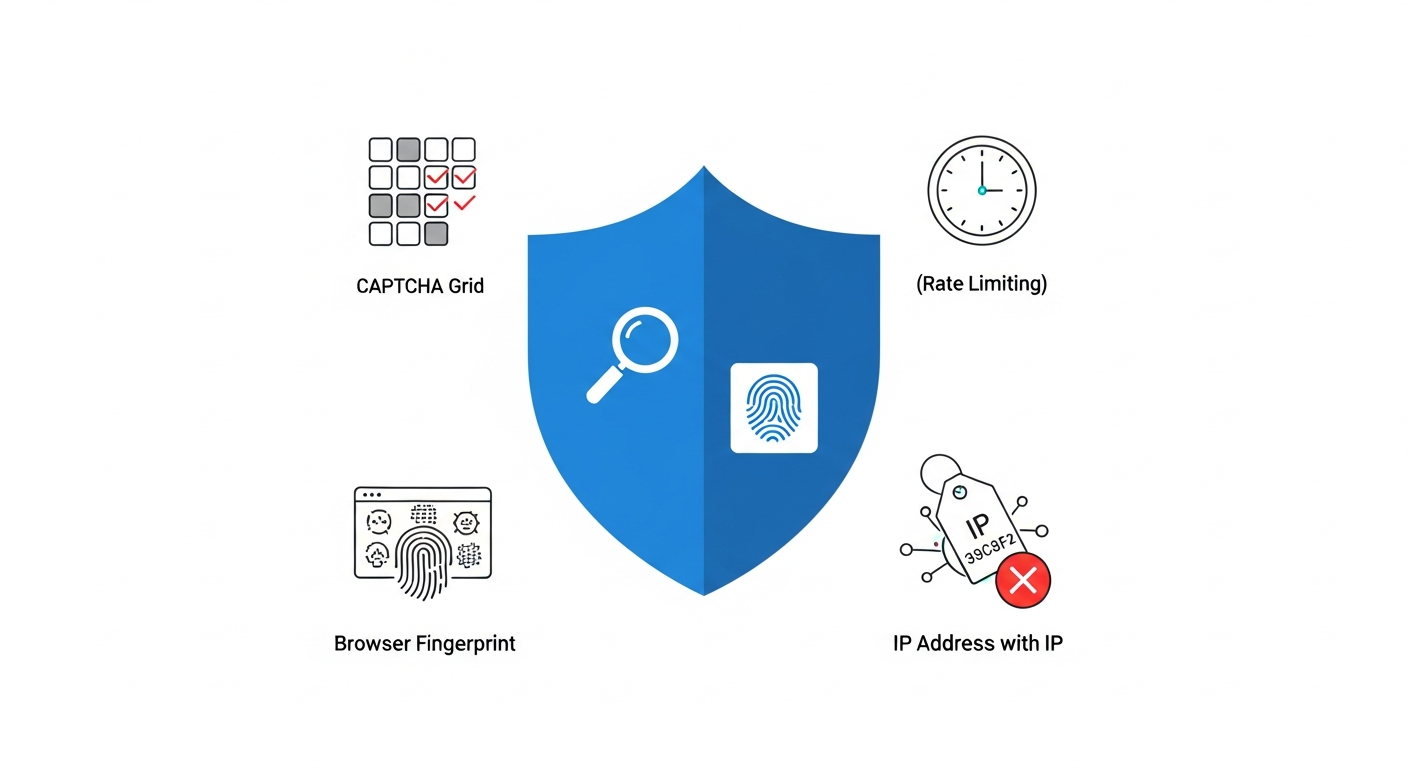
Detection Recommendations
Organizations need layered approaches rather than single-point solutions:
- Device fingerprinting to identify returning actors regardless of IP
- Behavioral analytics to spot patterns inconsistent with normal users
- Anomaly detection for unusual geographic or temporal access patterns
- Rate limiting based on behavioral signals rather than just IP addresses
How to Use Proxy Browsers Safely and Responsibly
Using proxy browsers ethically requires respecting terms of service, local laws, and data-protection regulations. The technology itself enables both legitimate business operations and potential misuse—responsible users understand the difference.
Guidelines for Individuals
- Avoid unknown free proxy apps: Many free plan offerings include hidden costs like data harvesting or malware. A truly absolutely free service often monetizes through your sensitive data or bandwidth.
- Review permissions carefully: Proxy browser apps requesting excessive permissions may steal data or perform proxy misuse.
- Verify encryption: Ensure HTTPS appears in your address bar, especially when handling financial or personal information on public networks.
- Don’t access dark web or onion websites through untrusted proxies: Tor browser provides purpose-built security for such use cases that random proxy browsers cannot match.
Choosing the Right Configuration
Selecting appropriate settings matters as much as choosing the tool:
- Proxy type: Residential for consumer-like browsing, mobile for app testing
- Rotation mode: Rotating for scraping data at scale, sticky for session-dependent tasks
- Geo-targeting: Country and city-level targeting for localized testing
SimplyNode supports safer use through ethically-sourced IPs, pay-as-you-go pricing with no long-term lock-in, HTTPS and SOCKS5 support, and clear usage documentation that helps teams configure proxy browsers correctly.
How to Choose the Right Proxy Network for Your Proxy Browser
The proxy browser is only as good as the proxy infrastructure behind it. Even the best proxy browser apps underperform when connected to unreliable or poorly-sourced proxy servers.
Evaluate Proxy Quality
Key performance metrics to assess:
- Success rate: What percentage of requests complete without errors?
- Response time: Average latency for different target sites and regions
- Stability under load: Performance consistency during high-volume operations
For tasks like scraping, ad verification, or managing multiple accounts, inconsistent proxies create failed requests and wasted time.
Assess IP Diversity
Global coverage determines what use cases you can support:
- Number of countries and cities available
- Total pool size (major providers offer millions of IPs)
- Rotation logic to avoid reusing the same IPs too frequently
Providers with limited pools see their IPs flagged more quickly as sites detect repeated access patterns.
Verify Compliance and Ethics
Reputable providers clearly state how they source residential and mobile IPs. Look for:
- Opt-in consent from device owners
- Transparent privacy practices
- Compliance with data protection regulations
- Clear terms prohibiting illegal use
Third party proxies from unknown sources may include devices enrolled without owner knowledge—creating legal exposure.
SimplyNode Alignment
SimplyNode addresses these criteria with:
- Residential and mobile proxies from ethically-sourced networks
- Granular geo-targeting by country and city
- Rotating and sticky session support
- Flexible pay-as-you-go plans with no traffic expiration
- HTTPS and SOCKS5 protocol support for diverse proxy configurations
These capabilities suit the 2026 business landscape where compliance, flexibility, and reliability define successful proxy operations.
Proxy Browsers in Corporate and Supply Chain Security
Security and risk teams increasingly track proxy browser usage inside companies and among vendors. The same tools that enable legitimate work also create visibility gaps and potential compliance violations.
Internal Risks
Employees may use proxy browsers to:
- Bypass corporate content filters to access restricted sites
- Access shadow IT services without security team awareness
- Conduct unauthorized competitive intelligence
- Hide browsing history from monitoring systems
Unmanaged proxy browser usage creates blind spots in security monitoring and potential data exfiltration paths.
Third-Party Risks
Vendors and contractors logging into corporate dashboards via unvetted proxies obscure the true source of access. This complicates:
- Incident investigation and forensics
- Compliance with access logging requirements
- Detection of compromised vendor accounts
- Attribution of suspicious activities
Recommended Controls
Organizations should implement layered defenses:
- Network policies: Block known proxy services and monitor for proxy-like traffic patterns
- SSO restrictions: Require corporate identity for sensitive system access
- Device security baselines: Ensure managed devices meet security standards
- Access logging: Maintain comprehensive logs for administrative actions
Vendor Risk Assessment
Add proxy-related questions to vendor assessments:
- Does the vendor use proxy browsers for accessing your systems?
- What proxy providers does the vendor use?
- How does the vendor ensure proxy traffic complies with your security requirements?
Periodic log reviews can identify suspicious geographic patterns—like a US-based vendor suddenly accessing systems from Eastern Europe.
Legitimate Internal Use
For teams that genuinely need proxies—brand protection, ad verification, market research—IT should centrally provide and manage approved proxy infrastructure. SimplyNode offers the kind of transparent, compliant service that organizations can confidently deploy for these purposes.
SimplyNode and Proxy Browsers: How We Fit In
SimplyNode is not a proxy browser itself but a proxy infrastructure provider that powers many browser-based use cases. We provide the residential and mobile proxies that make proxy browsers effective for legitimate business operations.
Integration Capabilities
Customers integrate SimplyNode proxies into:
- Major anti-detect browsers for multi account management
- Automation frameworks like Puppeteer and Playwright for scraping data
- Custom tools for ad verification and competitive intelligence
- Standard browsers configured with proxy extensions
Technical Features
Relevant capabilities for proxy browser workflows include:
- Protocol support: HTTPS and SOCKS5 for broad compatibility
- Session types: Rotating and sticky sessions for different use cases
- Authentication: Simple methods suitable for browser configuration
- Performance: High uptime and fast response times for production workloads
Geo-Targeting Precision
City-level and country-level targeting enables workflows such as:
- Localized SEO checks to verify search rankings by region
- Marketplace monitoring across multiple countries
- Competitive intelligence from specific geographic markets
- Ad verification to confirm campaign delivery in target areas
Ethical and Compliance Focus
SimplyNode differentiates through:
- Ethically-sourced IPs with proper consent mechanisms
- No forced device participation or hidden bandwidth sharing
- Transparent pay-as-you-go pricing
- No long-term contract requirements
- Clear documentation for responsible use
Whether you’re running a best proxy browser setup for market research or need to browse anonymously for competitive analysis, SimplyNode provides the infrastructure to do so reliably and responsibly.
Ready to power your proxy browser workflows with quality residential and mobile proxies? Get Started with SimplyNode traffic packages and experience the difference ethical sourcing and flexible pricing make for your operations.
FAQ
Is a proxy browser the same as using a VPN in 2026?
A proxy browser routes only browser traffic through a proxy server, while a VPN encrypts and routes most or all device traffic at the operating systems level. Proxy browsers offer more granular control for tasks like scraping or multi-accounting where you need different IPs per tab or profile. VPNs provide broader protection for general online privacy and remote access needs. Both can be combined, but organizations should carefully manage this configuration to maintain visibility into traffic patterns.
Can I use a proxy browser safely on public Wi-Fi?
Proxy browsers can improve privacy on public Wi-Fi when combined with HTTPS connections and a reputable proxy provider. However, you should avoid logging into sensitive financial or corporate systems through untrusted proxy browser apps from unknown developers. Always verify HTTPS appears in the address bar and use additional protections like MFA for important accounts. Similar apps may claim security but lack proper implementation.
Which proxies work best with proxy browsers: residential, mobile, or datacenter?
Residential proxies are ideal for most consumer-like browsing and web scraping because they originate from real ISP networks and appear as genuine users. Mobile proxies excel for mobile ad testing and app verification where carrier IPs are expected. Datacenter proxies offer speed advantages but get flagged more easily by sophisticated detection systems on popular websites. For high-value tasks like ad verification, brand protection, and market research in 2026, residential and mobile proxies deliver better success rates. SimplyNode specializes in these proxy types, with seamless integration for other proxy browsers and anti-detect tools.
Do proxy browsers guarantee complete anonymity?
No tool can guarantee complete anonymity. Browser fingerprints, cookies, account behavior, and browsing session patterns can still reveal identifying information even when your IP is masked. Advanced anti-detect browsers combined with quality proxies significantly reduce tracking, but they require correct configuration and ongoing attention. For better protection, combine technical tools with good operational security: use unique accounts, minimize sharing of personal data, and avoid patterns that link your activities. The Tor network provides stronger anonymity guarantees for users who need to access onion websites or require protection against state-level adversaries.
How much does it cost to run a proxy browser setup for business use?
Costs depend on three main factors: proxy browser licensing (free plan options exist, though the cheapest paid plan tiers typically offer advanced features), proxy traffic volume, and required geographic locations. Small teams often start with a few gigabytes of residential traffic per month, scaling up as scraping, monitoring, or ad verification workloads grow. Enterprise operations may consume terabytes monthly. SimplyNode’s pay-as-you-go pricing with no traffic expiration is well-suited for teams that want to experiment without long-term commitments, allowing you to purchase traffic and use it at your own pace.

%20-%202026-05-29T113134.620.png)
%20-%202026-05-28T123409.485.png)
%20-%202026-05-27T175112.286.png)
%20-%202026-05-26T134040.303.png)
%20-%202026-05-21T164357.956.png)
%20-%202026-05-21T162719.912.png)
%20-%202026-05-19T120136.626.png)
%20-%202026-05-18T110557.344.png)
%20-%202026-05-15T113858.229.png)
%20-%202026-05-14T121851.922.png)
%20-%202026-05-13T120005.619.png)
%20-%202026-05-12T112504.017.png)
%20-%202026-05-11T112454.822.png)
%20-%202026-05-07T105244.165.png)
%20-%202026-05-05T121326.455.png)
%20-%202026-04-30T132926.682.png)
%20-%202026-04-29T122656.668.png)
%20-%202026-04-28T165006.557.png)
%20-%202026-04-27T151422.596.png)
%20-%202026-04-24T134808.219.png)
%20-%202026-04-23T131230.882.png)
%20-%202026-04-22T111352.506.png)
%20-%202026-04-21T115725.855.png)
%20-%202026-04-20T131158.661.png)
%20-%202026-04-10T112244.119.png)
%20-%202026-04-09T111424.150.png)
%20-%202026-04-08T130405.235.png)
%20-%202026-04-07T113530.055.png)
%20-%202026-04-06T113015.908.png)
%20-%202026-04-02T120940.360.png)
%20-%202026-04-01T144424.516.png)
%20-%202026-03-30T112807.229.png)
%20-%202026-03-26T160000.403.png)
%20-%202026-03-26T113412.170.png)
%20-%202026-03-25T110333.022.png)
%20-%202026-03-23T125824.589.png)
%20-%202026-03-19T135903.501.png)
%20-%202026-03-19T114712.472.png)
%20-%202026-03-18T142314.362.png)
%20-%202026-03-17T135837.094.png)
%20-%202026-03-16T113750.118.png)
%20-%202026-03-13T134616.799.png)
%20-%202026-03-11T133856.227.png)
%20-%202026-03-10T124412.864.png)
%20(100).png)
%20(99).png)
%20(98).png)
%20(97).png)
%20(96).png)
%20(95).png)
%20(94).png)
%20(92).png)
%20(91).png)
%20(90).png)
%20(90).png)
%20(89).png)
%20(88).png)
%20(87).png)
%20(86).png)
%20(85).png)
%20(84).png)
%20(83).png)
%20(82).png)
%20(81).png)
%20(80).png)
%20(79).png)
%20(78).png)
%20(77).png)
%20(76).png)
%20(75).png)
%20(74).png)
%20(73).png)
.png)
.png)
.png)
.png)
.png)
%20(72).png)
%20(70).png)
%20(68).png)
%20(66).png)
%20(64).png)
%20(63).png)
%20(62).png)
%20(60).png)
%20(59).png)
%20(58).png)
%20(57).png)
%20(52).png)
%20(51).png)
%20(49).png)
%20(48).png)
%20(46).png)
%20(45).png)
%20(44).png)
%20(43).png)
%20(42).png)
%20(41).png)
